this blog is providing information and tutorial about ethical hacking. cybersecurity, cybercrime awareness. cybercrime investigation, cybercrime detection, information security.!
Monday, November 28, 2022
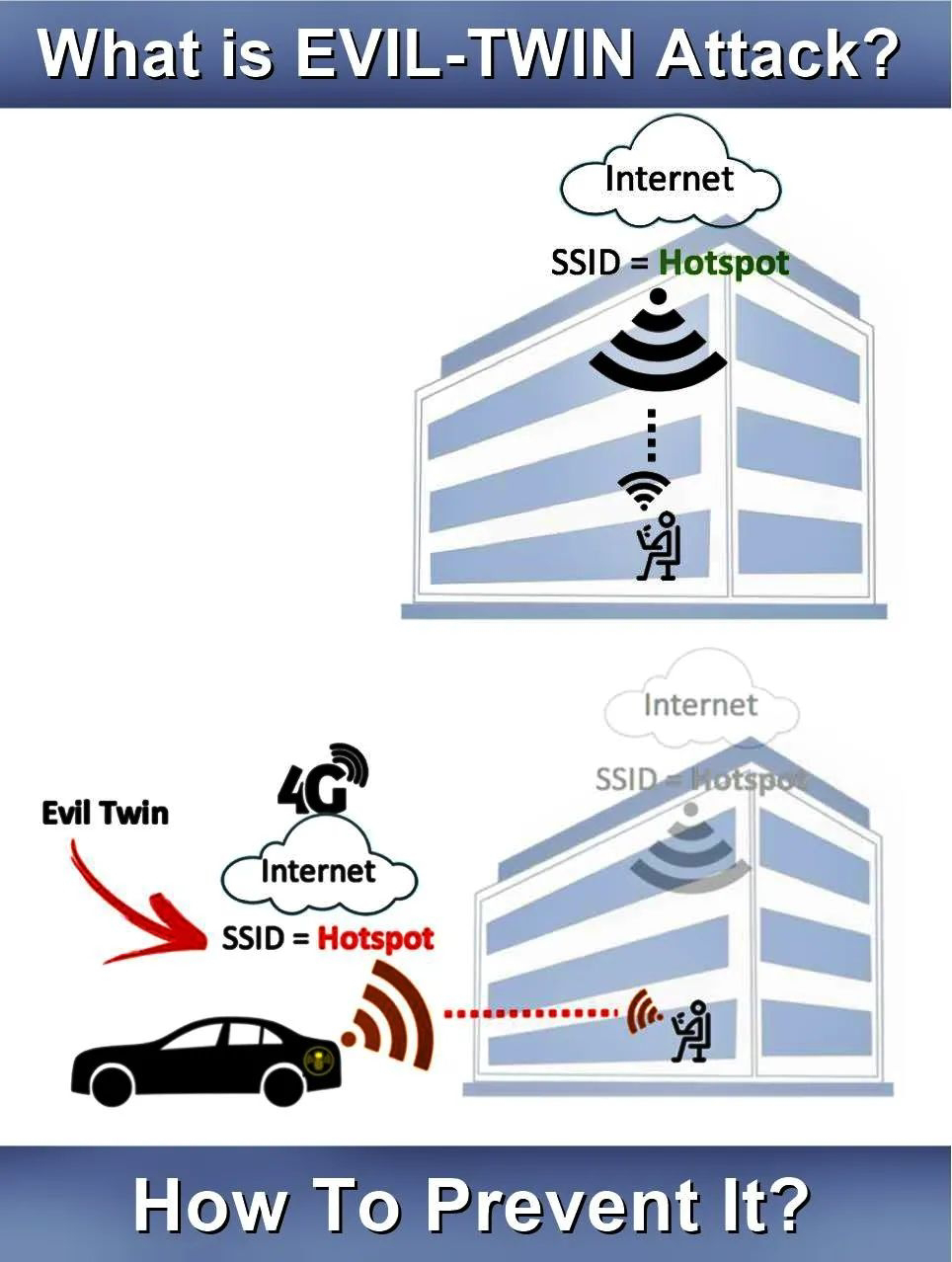
Evil Twin attack
Tuesday, November 15, 2022
view of PenTesting
In this post, I am trying to present you an holistic view of real-life IT penetration testing.
If you want to gain assurance in your organisation’s vulnerability assessment and management processes through a realistic simulation of a hacker attack, then IT penetration testing is a MUST. There is no doubt about that.
When you do that you get a number of benefits immediately:
You get a good Vulnerability Assessment within your IT network
Potential attacker’s entry points become transparent to you.
Your risk posture improves as most of exploitable vulnerabilities are identified.
Red/Blue Team gets practical exercise to test detection capabilities in real-time.
Security level of the investigated systems become measurable.
Compliance requirements (e.g. national regulations, GDPR, TISAX) for mandatory pentesting is fulfilled, if it done by third-party/consultants' pentesters.
You also receive a number of important recommendations regarding the improvements to be made to your information security and respective guidelines
In the hindsight, the pentesting is nothing but the real-life simulation of damages which might be carried out malicious threat actors.
My personal point of view is that--
Risk analysis of cyber-attacks are usually carried out on the basis of theoretical assessments only. The implementation of a Penetration Test is an ideal supplement to it, as it enables a real measurement of the resistance capability of your IT environment. Once the important vulnerabilities are confirmed and based on these findings, you can actually make a realistic risk assessment.
In the elaborated scheme of Pentesting, your Purple Team is the result of the collaboration between your Blue Team and the Red Team and can simulate Advanced Persistent Threats (APT).
As the lower-portion of the picture shows, the third party consultants can offer the various level of IT Penetration Testing services. It is you to make the judgment about which level of Pentesting your company needs at a given point in time. This picture also depicts the actual steps of pentesting process you/pentesters would need to undergo in real-life.
From your point of view, you can seek the pentesting of one or all of the following:
@) IT Pentesting
@) OT Pentesting
@) Platform Pentesting
This picture also depicts the actual steps of pentesting process you/pentesters would need to undergo in real-life. Let me brief you about.
1. Scope Qualification : You select all the assets which are in-the-scope of the Penetration Testing exercise/assignment and mark in written.
2. Kick-off : You meet all the involved stakeholders. You also introduce them into the scoped assets.
3. Execution of Penetration Test : You carry out real penetration tests against all the scoped assets, based on standardized methodology
4. Analysis & Report : You prepare and deliver a 'Penetration Test Report' officially with all the major recommendations clearly mentioned in it.
5. Improvement Workshop (Optional) : You may also carry out a technical workshop to help the defenders in mitigating all the risks involved with vulnerable assets.
6. Retest after Mitigation phase (Optional) : You may also carry out one more rounds of pentesting-attacks, to ensure that all the vulnerabilities which were found have actually been fixed or not
what is pyramid of pain?
Pyramid of Pain, a concept that was first introduced in 2013 by cybersecurity expert David J Bianco. The “pain” in his concept refers to the difficulty faced by the adversary in succeeding if they are denied certain indicators.
Pyramid of pain consists of six types of loCs that are arranged in increasing order of the impact on the adversary and effort of the analyst respectively.
Pyramid of pain represents the types of indicators that the analyst must look out to detect the activities of an adversary as well as the amount of pain that the adversary needs to adapt to pivot and continue with the attack even when the indicators at each level are being denied.
As the graphic indicates, it is trivial for the adversary to manipulate a hash value to bypass a detection engine that matches based on hash.
However, adding controls that restrict tactics, techniques, and procedures (TTPs) makes it very tough for them to overcome. I am a big believer in adding as many of these controls as possible; thus, adding a multiplier effect for each defensive capability.
Pretty cool stuff!
BUT, Why Are TTPs Placed At The Top?
Classical AV/FW Approach
The current approach used by companies to deal with cyber-attacks is insufficient. This is mainly caused by customers, enterprises, which believe that if they deploy an Anti-Virus solution combined with a Firewall and some additional automatic tools, their cybersecurity is sufficient in order protect from cyber threats.
What they don't wanna believe is that these cyber defenses are usually easily bypassed by a motivated and determined attacker.
For example, most Anti-viruses are helpless against in-memory only malware or malware signed by a legitimate code signing certificate which might have been stolen by the attacker. Similarly, Firewalls and other network monitoring measures can be bypassed by camouflaging the malicious traffic in such a way that the traffic generated by the malware seems legitimate or inaccessible by the monitoring tools.
It’s common to see malware successfully communicating over the HTTP protocol which mimics normal user’s behavior. In addition, the traffic can be encoded or encrypted making it difficult to analyze in an automatic approach.
Finally, even the anti- Zero-Day countermeasures can be bypassed by attackers as some of those solutions are freely (i.e. EMET) or easily accessible for well-resourced attackers. Given enough motivation, a determined attacker could install a defense mechanism that is needed to be bypassed and study it until a successful exploit is developed.
This is worst approach!
Automated Security Approach
Another approach used within the industry to combat intrusion is, to rely entirely on security software or appliances which use a pre-compiled and constantly updated list of Indicators of Compromise (IOCs). Although this approach is better than classic AV/FW approach and bit more comprehensive, yet it is still not up to the mark. It is not sufficient, because it is reactive by its nature.
Why?
Because IOCs are compiled after the analysis of certain infections somewhere else and thus can only provide protection against KNOWN threats.
Moreover, these IOCs can be accessible to any motivated threat actor and therefore be used, to adjust its tools to successfully perform attack campaigns in the future. That's why, relying on these static indicators as a mechanism to identify APTs will have low impact on any broader malicious operation that is carried out by a determined and sophisticated threat.
Do you understand it clearly?
TTP based Detection & Response
This is exactly the point where the importance of fighting the threat actor’s TTPs rather than static IOCs becomes obvious. Only thing required is that you understand well the correlation between each pain area of this Pyramid of Pain and the degree of effort that would be needed by the attacker to overcome the obstacles put by defenders.
By combining classical approaches with a more dynamic and intensive behavioral analysis of Advanced Persistent Threats, you can create a more comprehensive profile of threats which will allow you to minimize the risk of being compromised.
This also means that instead of relying on automatic security solutions the defender needs to first understand the Tactics, Techniques, and Procedures of its enemy and then start planting obstacles which could prevent from a highly-motivated attacker, such as an APT.
How Can This Be Achieved?
This could be achieved by:
Constantly studying attacks which are occurring in the wild,
analyzing their TTPs, building and training blue teams to understand the mindset of an Advanced Persistent Threat actor, engaging the blue team with a red team in order to keep up with sharp and decent skills for detecting intrusion attempts and implementing prevention mechanisms.
While there is no silver bullet to cyber-attacks, causing a significant amount of pain for an adversary the defender can drastically reduce the likelihood of a successful breach.
Therefore, it is important to fully understand the concept of TTPs as exposing TTP patterns will have the most impact on the adversary.
Evil Twin attack
Evil Twin Attack is attack is frequently carried upon wireless access points with malicious intentions. This attack happens when...
-
A typical organization is divided into operational, middle, and upper level. The information requirements for users at each level differ. ...
-
A cyber security risk assessment is the process of identifying, analysing and evaluating risk. It helps to ensure that the cyber security ...


