this blog is providing information and tutorial about ethical hacking. cybersecurity, cybercrime awareness. cybercrime investigation, cybercrime detection, information security.!
No posts with label https://www.facebook.com/Ethhicalhacking/. Show all posts
No posts with label https://www.facebook.com/Ethhicalhacking/. Show all posts
Subscribe to:
Posts (Atom)
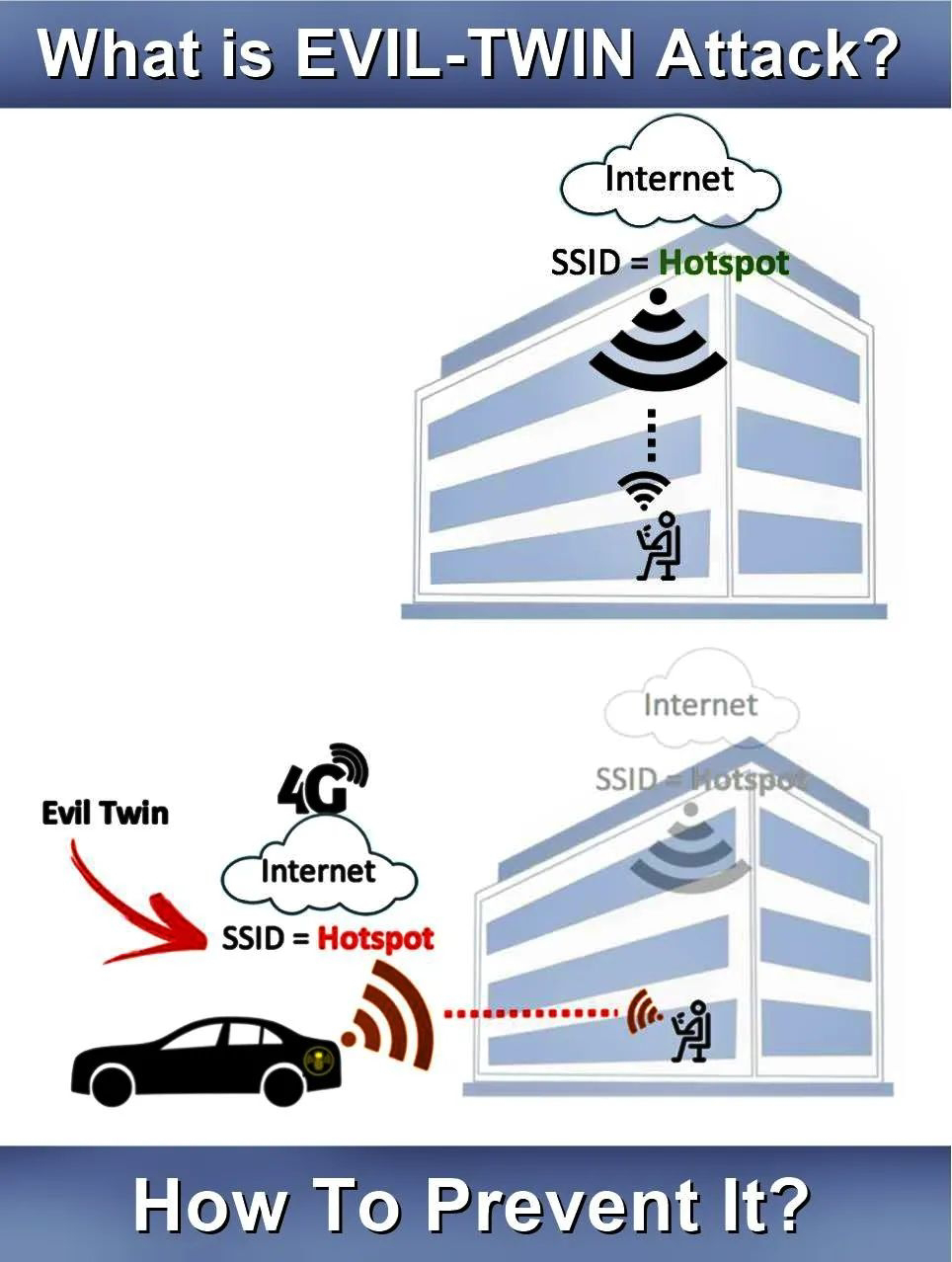
Evil Twin attack
Evil Twin Attack is attack is frequently carried upon wireless access points with malicious intentions. This attack happens when...
-
A typical organization is divided into operational, middle, and upper level. The information requirements for users at each level differ. ...
-
How to Know Who Logged into your computer and when? In Windows, there is one in-built too will records all events in your computer ...
