Maa cyber security group
this blog is providing information and tutorial about ethical hacking. cybersecurity, cybercrime awareness. cybercrime investigation, cybercrime detection, information security.!
Monday, November 28, 2022
Evil Twin attack
Tuesday, November 15, 2022
view of PenTesting
In this post, I am trying to present you an holistic view of real-life IT penetration testing.
If you want to gain assurance in your organisation’s vulnerability assessment and management processes through a realistic simulation of a hacker attack, then IT penetration testing is a MUST. There is no doubt about that.
When you do that you get a number of benefits immediately:
You get a good Vulnerability Assessment within your IT network
Potential attacker’s entry points become transparent to you.
Your risk posture improves as most of exploitable vulnerabilities are identified.
Red/Blue Team gets practical exercise to test detection capabilities in real-time.
Security level of the investigated systems become measurable.
Compliance requirements (e.g. national regulations, GDPR, TISAX) for mandatory pentesting is fulfilled, if it done by third-party/consultants' pentesters.
You also receive a number of important recommendations regarding the improvements to be made to your information security and respective guidelines
In the hindsight, the pentesting is nothing but the real-life simulation of damages which might be carried out malicious threat actors.
My personal point of view is that--
Risk analysis of cyber-attacks are usually carried out on the basis of theoretical assessments only. The implementation of a Penetration Test is an ideal supplement to it, as it enables a real measurement of the resistance capability of your IT environment. Once the important vulnerabilities are confirmed and based on these findings, you can actually make a realistic risk assessment.
In the elaborated scheme of Pentesting, your Purple Team is the result of the collaboration between your Blue Team and the Red Team and can simulate Advanced Persistent Threats (APT).
As the lower-portion of the picture shows, the third party consultants can offer the various level of IT Penetration Testing services. It is you to make the judgment about which level of Pentesting your company needs at a given point in time. This picture also depicts the actual steps of pentesting process you/pentesters would need to undergo in real-life.
From your point of view, you can seek the pentesting of one or all of the following:
@) IT Pentesting
@) OT Pentesting
@) Platform Pentesting
This picture also depicts the actual steps of pentesting process you/pentesters would need to undergo in real-life. Let me brief you about.
1. Scope Qualification : You select all the assets which are in-the-scope of the Penetration Testing exercise/assignment and mark in written.
2. Kick-off : You meet all the involved stakeholders. You also introduce them into the scoped assets.
3. Execution of Penetration Test : You carry out real penetration tests against all the scoped assets, based on standardized methodology
4. Analysis & Report : You prepare and deliver a 'Penetration Test Report' officially with all the major recommendations clearly mentioned in it.
5. Improvement Workshop (Optional) : You may also carry out a technical workshop to help the defenders in mitigating all the risks involved with vulnerable assets.
6. Retest after Mitigation phase (Optional) : You may also carry out one more rounds of pentesting-attacks, to ensure that all the vulnerabilities which were found have actually been fixed or not
what is pyramid of pain?
Pyramid of Pain, a concept that was first introduced in 2013 by cybersecurity expert David J Bianco. The “pain” in his concept refers to the difficulty faced by the adversary in succeeding if they are denied certain indicators.
Pyramid of pain consists of six types of loCs that are arranged in increasing order of the impact on the adversary and effort of the analyst respectively.
Pyramid of pain represents the types of indicators that the analyst must look out to detect the activities of an adversary as well as the amount of pain that the adversary needs to adapt to pivot and continue with the attack even when the indicators at each level are being denied.
As the graphic indicates, it is trivial for the adversary to manipulate a hash value to bypass a detection engine that matches based on hash.
However, adding controls that restrict tactics, techniques, and procedures (TTPs) makes it very tough for them to overcome. I am a big believer in adding as many of these controls as possible; thus, adding a multiplier effect for each defensive capability.
Pretty cool stuff!
BUT, Why Are TTPs Placed At The Top?
Classical AV/FW Approach
The current approach used by companies to deal with cyber-attacks is insufficient. This is mainly caused by customers, enterprises, which believe that if they deploy an Anti-Virus solution combined with a Firewall and some additional automatic tools, their cybersecurity is sufficient in order protect from cyber threats.
What they don't wanna believe is that these cyber defenses are usually easily bypassed by a motivated and determined attacker.
For example, most Anti-viruses are helpless against in-memory only malware or malware signed by a legitimate code signing certificate which might have been stolen by the attacker. Similarly, Firewalls and other network monitoring measures can be bypassed by camouflaging the malicious traffic in such a way that the traffic generated by the malware seems legitimate or inaccessible by the monitoring tools.
It’s common to see malware successfully communicating over the HTTP protocol which mimics normal user’s behavior. In addition, the traffic can be encoded or encrypted making it difficult to analyze in an automatic approach.
Finally, even the anti- Zero-Day countermeasures can be bypassed by attackers as some of those solutions are freely (i.e. EMET) or easily accessible for well-resourced attackers. Given enough motivation, a determined attacker could install a defense mechanism that is needed to be bypassed and study it until a successful exploit is developed.
This is worst approach!
Automated Security Approach
Another approach used within the industry to combat intrusion is, to rely entirely on security software or appliances which use a pre-compiled and constantly updated list of Indicators of Compromise (IOCs). Although this approach is better than classic AV/FW approach and bit more comprehensive, yet it is still not up to the mark. It is not sufficient, because it is reactive by its nature.
Why?
Because IOCs are compiled after the analysis of certain infections somewhere else and thus can only provide protection against KNOWN threats.
Moreover, these IOCs can be accessible to any motivated threat actor and therefore be used, to adjust its tools to successfully perform attack campaigns in the future. That's why, relying on these static indicators as a mechanism to identify APTs will have low impact on any broader malicious operation that is carried out by a determined and sophisticated threat.
Do you understand it clearly?
TTP based Detection & Response
This is exactly the point where the importance of fighting the threat actor’s TTPs rather than static IOCs becomes obvious. Only thing required is that you understand well the correlation between each pain area of this Pyramid of Pain and the degree of effort that would be needed by the attacker to overcome the obstacles put by defenders.
By combining classical approaches with a more dynamic and intensive behavioral analysis of Advanced Persistent Threats, you can create a more comprehensive profile of threats which will allow you to minimize the risk of being compromised.
This also means that instead of relying on automatic security solutions the defender needs to first understand the Tactics, Techniques, and Procedures of its enemy and then start planting obstacles which could prevent from a highly-motivated attacker, such as an APT.
How Can This Be Achieved?
This could be achieved by:
Constantly studying attacks which are occurring in the wild,
analyzing their TTPs, building and training blue teams to understand the mindset of an Advanced Persistent Threat actor, engaging the blue team with a red team in order to keep up with sharp and decent skills for detecting intrusion attempts and implementing prevention mechanisms.
While there is no silver bullet to cyber-attacks, causing a significant amount of pain for an adversary the defender can drastically reduce the likelihood of a successful breach.
Therefore, it is important to fully understand the concept of TTPs as exposing TTP patterns will have the most impact on the adversary.
Thursday, August 18, 2022
How much safe your VPN is?
Well, the answer is...It depends!
You use a reliable VPN to be sure that you remain safe & secure while you browse the internet. When you don't want to be snooped on by government agencies or other companies, then you use a VPN. When you want to access the websites which have been blocked by your government, then you use VPN. When you don't want your ISP to track your online activities, you use VPN.
**VPN is a great tool, but they come with a caveat. **
Not all VPNs are equal. For example, if you are using a free VPN then you might be compromising your security as well as anonymity.
VPNs are used by individuals and the corporates as well by creating a private browsing session for each user.
Suppose you are travelling to a remote area and you need to connect to your company's network. In that case, you might need to connect to public Wi-Fi first. But such public Wi-Fi may let other users of that network to eavesdropping on what you are trying to do online. You should surely use a VPN in situations like this, because a VPN creates a secure tunnel between your computer/laptop and the VPN server which will hide your all online activities and location too.
Indeed, VPN allows you to protect your online privacy, and prevent your ISP to track your online activities. All VPNs work by connecting your device to VPN server and then bypassing your internet traffic through your VPN service provider's internet connection.
This process successfully hides your browsing information...
The very same process does not let any MiTM attacker to gather or monitor your online activities too.
___
Though Google Chrome offers you 'InCognito' mode. Microsoft Edge, Firefox offer 'Private Browsing' modes. But you should not make a mistake of assuming that these modes are replacement of a VPN.
These modes may not let data from being stored on your local device or computer. These modes may not save your browsing history, for example. But it does not mean that no one can track you. Of course, your ISP can still track you. The vendors whose plugins are working in such modes, may also track your behavior.
On a side note, Opera does have an inbuilt 'VPN' feature.
___
1. Free VPN tools can compromise your security.
You may not realize that if you are using some Free VPN service, then the application you are using to connect with VPN server may not be safe. It is very much possible that such apps may contain malware within themselves. Such malware could also be used by cyber-attackers to steal your data, gain unauthorized access to your data or machine, or launch a malicious attack on your system. In 2016, a paper was published on VPN tools' privacy and security issues for Android devices. ICSI Network and Security Group had found that as many as 283 Android VPN apps contained some form of malware presence. So many of these apps were asking for too many of permissions, quite more than they required.
Same can be true of all sort of VPN applications...You need to be watchful here.
**2. Free VPN tools track your online activity. **
The same study found that 72% of Free VPN services were using third-party tracking tools in their software. It means those third-parties were collecting users information and sell it for money to the highest bidders. The objective was to allow targeted advertising to those users by online-advertisers.
A VPN is supposed to protect your activity while you are browsing the internet. But they were doing the opposite by tracking your online activities.
Some free VPN tools totally hide this information about -- whether they share or sell user data, however others service providers may mention this in their privacy policies. A normal user ironically never tends to read their privacy policies.
3. Free VPN tools limit data usage too.
Let us take an example, that you want to watch a movie from Netflix, but it is not available in your country or region, because of any restriction. VPN would let you do that. But in case of using FREE VPNs, they may place some cap or limitation of the amount of data you can use through their tool. This limitation can be daily or monthly. There may be other types of limitations too.
Thus, if you want to protect your data or mask your location for a considerable length of time, then Free VPNs are not for you.
4. Free VPNs slow down users’ internet speed.
They do. I have seen that even paid VPN services succumbing to slow internet speed many a times. They do slow the internet-speed available to you, because ultimate objective is to push you to buy their paid version of the service.
5. Free VPN tools target users with ads.
These services need revenues to sustain their operations. If they cannot charge in case of FREE VPN, then they use direct advertising to boost their revenues. The ads are served to you, without even your permission. Ads not only slow down the internet speed further, they also can distract you from doing some productive work.
The presence of ads on a free VPN service is by default a privacy concern because it is likely the provider is sharing your online activity with third-party services.
___
Different vendors have different parameters for delivering security to you.
If a VPN provider is ensuring your online privacy, providing transparent privacy policies, fixing data-leaks, and not tracking its users, then you can say that it is a 'safe' VPN.
The whole idea of VPN is to hide your IP address or disguise it. But sometimes, there can be some software bugs or coding errors, that may generate flows which may result in leaking your IP address or location. That's why, when you check online review of customers on internet, you should look for any history of IP-address leakage. If it was there, when it happened, how, or how it was stopped.
There should be ZERO Logging by VPN. They should not collect or log any data you or other users are sharing on such networks. They should not log any log-in credentials, files you have downloaded, website you visited, or your search queries. It is essential to maintain your anonymity. You don't want your VPN tools to have any ability to record or store such information even on your computer. If it does, then a malicious attacker can compromise the application and take out all the information, before it is purged.
You should activate the Multi-factor Authentication (MFA) feature of these VPN applications. This extra security feature is mandatory in modern times of cyber-crimes.
When a malfunction happens, your device using the VPN typically goes back to using its default internet connection. This happens automatically. Worse, this also usually happens without you being aware and your IP address gets leaked with a few seconds.
That's why, you should surely check that your VPN application has a VPN Kill-switch. This feature is important because it will result in automatic exit of specific programs that were using VPN internet connect. This feature comes very handy, when your VPN connection drops due to any reason. Most VPN services include one as part of the client application. When it detects a problem, the kill switch triggers and stop all of your device’s traffic from reaching the internet. It effectively kills your connection.
A VPN from a reliable & trustworthy service-provider should encrypt your data and online browsing history to shield them from hackers and ISPs.
Paid-versions of VPNs usually include ad-blocking tools, as well as features like malware protection and unlimited bandwidth, which keep your data secure.
Why is cyber security risk assessment so important?
A cyber security risk assessment is the process of identifying, analysing and evaluating risk. It helps to ensure that the cyber security controls you choose are appropriate to the risks your organisation faces.
Risk assessment is a process that includes:
* Identifying vulnerabilities, threats, and risks that can cause any
sort of damage to the organization
* Estimating the probability of risks being realized
* Defining mitigation priorities by risk severity and the likelihood
of occurrence
In risk management, assessment is preceded by framing (establishing the context of risks) and followed by responding to and monitoring these risks.
Without a risk assessment to inform your cyber security choices, you could waste time, effort and resources. There is little point implementing measures to defend against events that are unlikely to occur or won’t impact your organisation.
Likewise, you might underestimate or overlook risks that could cause significant damage. This is why so many best-practice frameworks, standards and laws – including the GDPR (General Data Protection Regulation) and DPA (Data Protection Act) 2018 – require risk assessments to be conducted.
Please understand very clearly that it is an ongoing process that helps you evaluate your security controls, detect issues, and estimate their impact.
5-Major Reasons For Conducting An Cyber/IT Risk Assessment:
1. To prevent hacks, data breaches, and data loss. A periodic review of cybersecurity controls allows you to detect and close off vulnerabilities before hackers can exploit them.
2. To examine network security. An independent risk assessment provides an unbiased examination of your network’s security controls. It helps you update knowledge on your protected environment, especially after significant changes like deploying new software, installing new hardware, or moving to a new location.
3. To improve decision-making. Determining the impact of discovered risks is an important part of a risk assessment. This information is useful for making further decisions related to cybersecurity: budgeting, planning improvements, prioritizing fixes, etc.
4. To reduce spending on cybersecurity. An assessment is a time- and cost-consuming procedure. But in the long term, it can save you from more severe losses by preventing data breaches, hacks, and compliance violations.
5. To ensure compliance. Risk management is part of many laws, regulations, and standards including NIST Special Publications, HIPAA, PCI DSS, and GDPR. Failing to comply with those that are relevant to your business may lead to substantial fines.
A REVIEW CHECKLIST FOR NETWORK SECURITY ANALYSIS
All network analyzers/sniffers have the ability to capture data from network. But most of them only do some simple statistics then throw pages of numbers to the users. Especially in a big network with heavy traffic, network administrators have to figure out a network problem even a simple one.
The Security Analysis is a perfect example. The Security Analysis is an analysis profile which has the power to detect the following network anomalies and attacks:
* ARP attack
* Worm activity
* DoS attack
* TCP port scanning
* Suspicious conversation
Review a Checklist of Analysis Tasks
There are a large number of tasks which a Security Analyst should perform. These tasks can be considered proactive or reactive.
Proactive methods include BASELINING network communications to learn the current status of the network and application performance. It can also be used to spot network problems before they are felt by the network users.
For example, identifying the cause of packet loss before it becomes excessive and affects network communications helps avoid problems before they are even noticed.
Reactive analysis techniques are employed after a complaint about network performance has been reported or when network issues are suspected. Sadly, reactive analysis is more common.
The following lists some of the analysis tasks that can be performed using Wireshark:
@@ Find the top talkers on the network
@@ Identify the protocols and applications in use
@@ Determine the average packets per second rate and bytes per second rate of an application or all network traffic on a link
@@ List all hosts communicating
@@ Learn the packet lengths used by a data transfer application
@@ Recognize the most common connection problems
@@ Spot delays between client requests due to slow processing
@@ Locate misconfigured hosts
@@ Detect network or host congestion that is slowing down file transfers
@@ Identify asynchronous traffic prioritization
@@ Graph HTTP flows to examine website referrals rates
@@ Identify unusual scanning traffic on the network
@@ Quickly identify HTTP error responses indicating client and server problems
@@ Quickly identify VoIP error responses indicating client, server or global errors
@@ Build graphs to compare traffic behavior
@@ Graph application throughput and compare to overall link traffic seen
@@ Identify applications that do not encrypt traffic
@@ Play back VoIP conversations to hear the effects of various network problems on network traffic
@@ Perform passive operating system and application use detection
@@ Spot unusual protocols and unrecognized port number usage on the network
@@ Examine the startup process of hosts and applications on the network
@@ Identify average and unacceptable service response times (SRT)
@@ Graph intervals of periodic packet generation applications or protocols
Networks vary greatly in the traffic seen. The number and type of network analysis tasks you can perform depends on your network traffic characteristics.
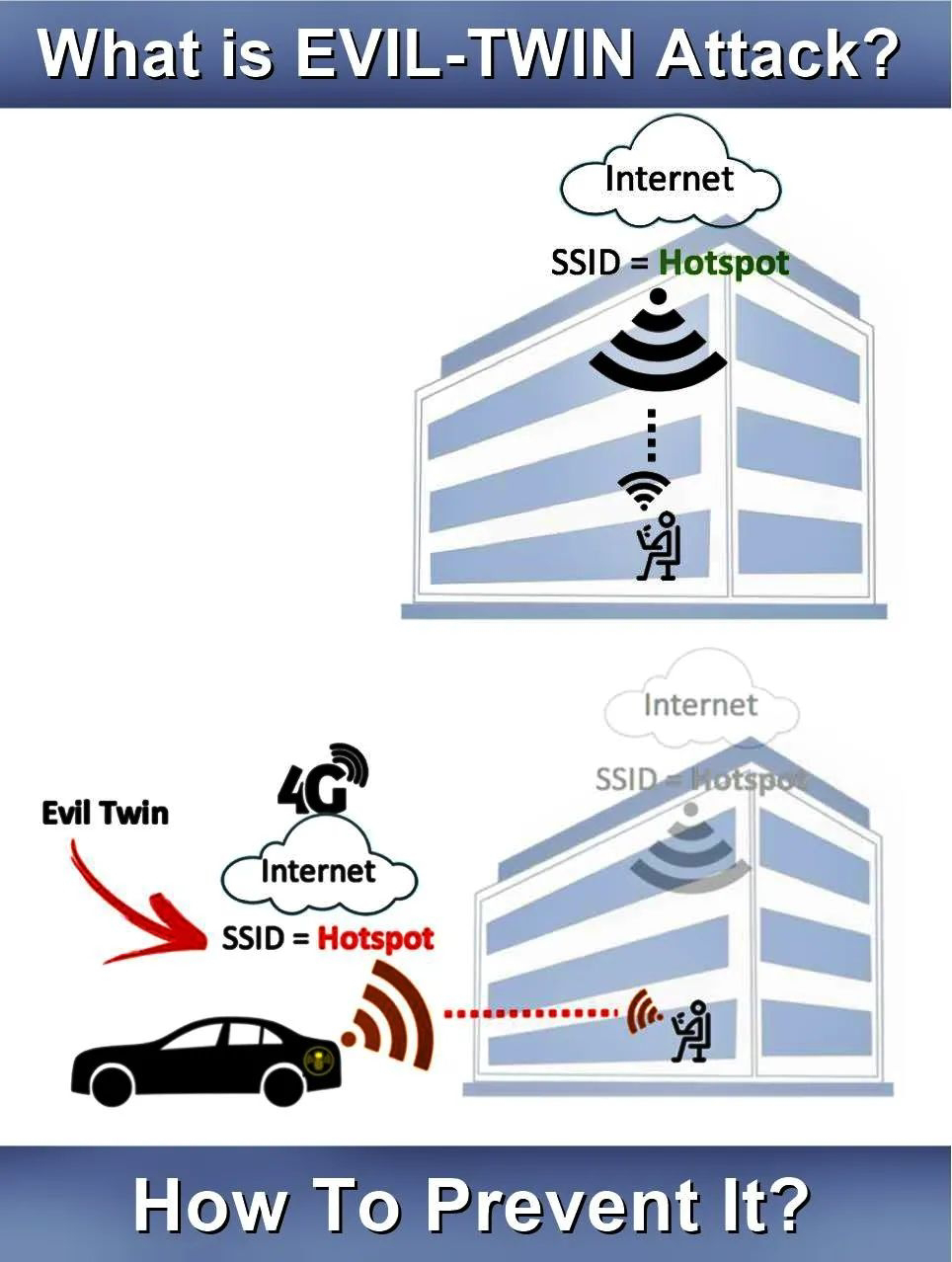
Evil Twin attack
Evil Twin Attack is attack is frequently carried upon wireless access points with malicious intentions. This attack happens when...
-
A typical organization is divided into operational, middle, and upper level. The information requirements for users at each level differ. ...
-
In this article, you will start with your first Android Testing. To guarantee quality of your Android application, you should follow the pr...




